Early this week, clients of Transnational Bank complained of slow and sometimes non-existent services.
It became clear later that the bank had been hacked and the hackers had disrupted the Bank’s systems demanding a ransom be paid.
“A bank in the republic of Kenya was hacked”, the hacker named @SzandorTigris announced on August 6th 2020.

He went on to publish the screenshots of the data that he has acquired, ‘still asking’ for ransom which eventually culminated in a link. He shared a link to the banks documents that he had stolen just 21 hours ago.
The bank has not responded up to now.
In February 20202, Transnational Bank was fully acquired by Access Bank of Nigeria.
In the five days that the bank’s systems were down, clients could not access ATM, Mobile and web banking. Activities at the branches were slow and undertaken ver an Excel Data that had been downloaded.

Transnational Bank later wrote after days of silence, ‘Dear Customer, we are pleased to inform you that the service downtime experienced on our online banking platforms has been restored. We regret the inconveniences caused. We thank you”.
However, this message was met with complaints of missing money.
Please systems are still down money already deducted from account, what is happening ? is there any ETR on the case? please @tnblkenya respond ?
— robert (@chepchiengrobe1) August 7, 2020
Please guys, have transferred money to my mpesa but not reflected while account had been deducted, Check out please
— robert (@chepchiengrobe1) August 6, 2020
https://twitter.com/NicholasLangat2/status/1291399071987630082?s=20
I did a transaction which failed, but checking the balance later shows me the money was withdrawn. Didnt receive in my mpesa
— Joe (@rotichj) August 6, 2020
The above complaints just show the extent of the damage done by the hacker.
Question is, do they still have access to the bank’s systems?
What is Transnational and Acess Bank’s doing to reclaim their systems?
Was Central Bank of Kenya (CBK) aware about the weak IT systems of this bank even as exposed through an Audit report by Ersnt & Young LLP?
This data leak is massive and the bank must come out and assure its clients.

The Audit
(Copied from Kenyanbusinessfeed.com)
An audit report prepared by the firm Ernst & Young LLP on the information and communication technology controls of Transnational Bank, paints a grim picture of the ICT system at the bank.
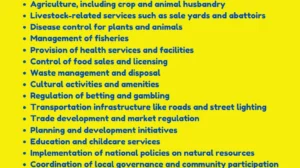
One of the revelations that caught the eyes of this KenyanBusinessFeed.Com editor was under ‘the inadequate password and security settings’. The report stated, ‘the passwords did not meet the minimum complexity requirements’. They also allowed ‘Concurrent multiple logins’, on the ‘Chapaa Popote, Chequepoint Truncation System, Paynet and Simba HR Cube systems’.
The second pointer to weak systems in the audit report was ‘inappropriate access to IT administrator role in Chequepoint and Simba HR Cube System’. The audit signed by EY Risk Advisory Leader for Eastern Africa Mr Robert J. Nyamu, stated that ‘business users had access to administrative IT rights and could create new users’. It also said, ‘review of inward cheque processing on the application, we observed as the user used the ‘Admin’ account to approve the cheque files after upload and adoption by the clearing clerk.
This ‘increase the risk of overriding controls within the application’, which could, lead to ‘unauthorized activities conducted on the payroll’.
The third weakness was ‘Lack of role monitoring of users and user activity in systems, which posed a ‘risk that application access violations and inappropriate transactions may not be identified in a timely manner”
The fourth weakness is ‘System issue with reset accounts on Chequepoint Truncation System. This posed the “risk of user intentionally or unintentionally interfering with financial information by gaining access to more than one user account on the application”.

The last risk was about the Server Room, where the auditors noted the weak access control of the server room.
“During the review of the server room, the following weaknesses were noted: The floor on the server room is raised using wooden material which is combustible. Other combustible materials noted include; the material used for the ceiling and a wooden plank lying on the floor. Combustible material was also observed in the area just outside the server room which is used as a storage area. There was no automatic fire suppression system in the server room. Environmental factors to be controlled in the server room e.g. temperature levels, dust levels, humidity levels, other gases etc. are not monitored. Temperature level is monitored manually by physically going to the server room. There is no warning sign prohibiting drinking, eating and smoking in the data center”.
Though Ersnt & Young LLP did the recommendations to improve on the above, it is highly unlikely that the bank has implemented them.